Securing Your Life
Now more than ever, keeping your personal information is an almost impossible task. Most of our information is likely already out in cyber space and we have no way to repossess it. What we can do is control the level of information we release moving forward and make changes or \”embellishes\” of current information to create confusion to those looking to capitalize on your information. Credit Card Fraud, Identity Theft, fake online profile, you name it.
It can happen to any of us!
Credit Bureaus
On May 24, the Economic Growth, Regulatory Relief and Consumer Protection Act made some changes to the federal law dictating consumer credit rules.
One which consumer advocates had been seeking for years, will allow consumers to “freeze” their credit files at the three major credit reporting bureaus — Equifax, Experian and TransUnion — without charge. Consumers can also “thaw” their files, temporarily or permanently, without a fee.
TransUnion Link – Experian Link – Equifax Link
Passwords
1… You need a secure way to store your passwords to all different websites you have. Do NOT store them in the browser you are using. I know it is convenient but it is also putting you at risk. There are several good programs for your computer of cell phone to securely storing you passwords.
2… Consider using abnormal or sarcastic answers to security questions. This would be very hard to replicate if someone was trying to hack or gain access to your account, who may already have all your information, but don\’t know you or your sense of humor.
3… The new trend which is being adopted by many sites are for pass \”phrases\” instead of pass words. This could be an entire sentence in order to log in to a website or program. If this is an option, we HIGHLY recommend using it. A good passphrase could be a line from your favorite movie or TV show, a popular saying in your circle of friends, etc. Something no one else would even be able to guess even if they knew you.
Home Network
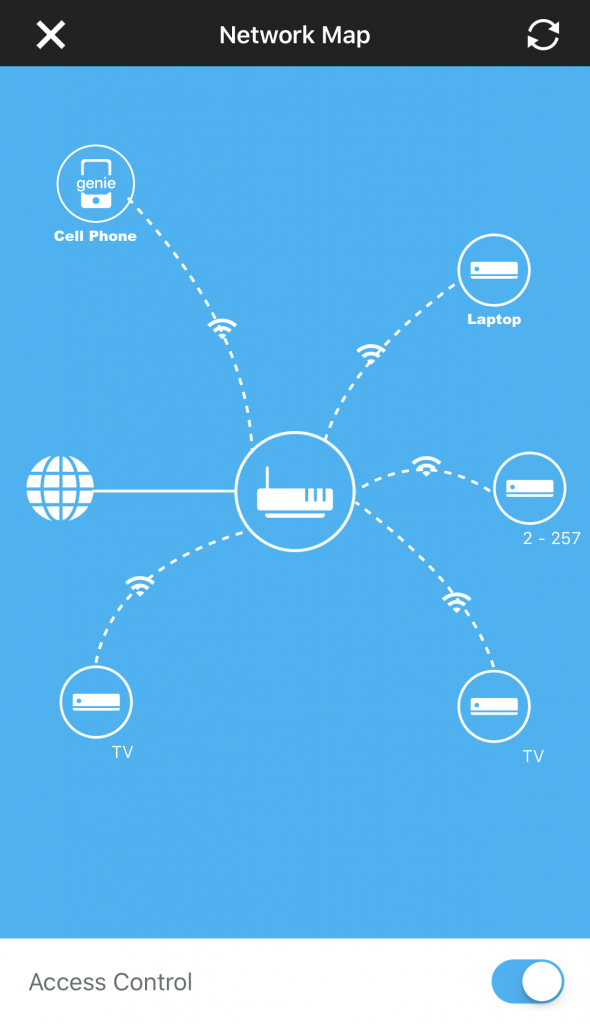
One thing you probably didn\’t realize about your home network. Almost all WiFi routers in homes today have software you can download to manage your connections, usage, and parental controls.
But one thing you may not know is that, if you are using your computer or cell phone in your home and close the laptop (not powering off) which puts it in a \”sleep mode\”, its connection to the WiFi router and Internet is still LIVE!! Meaning it can still be accessed by anyone able to tap into your router.
I noticed this when I downloaded the app on my phone (seen to the left) to control the usage by my children. When I closed my laptop and watched it go into sleep mode, the app still showed it as active and using data. What could it be doing while in sleep mode? So I attempted to Airdrop a file from my phone to my laptop and Whamo!!, the file was transferred successfully while the laptop was in sleep mode.
So I would highly recommend anyone at home or at work, when you device is not being used to turn off the WiFi on that device while you are not using it. Is this fool-proof? Probably not but it at least gives you a chance to make things more difficult for your device to be accessed through your router.
Another and more radical method is to turn off the WiFi router all together when not being used. It was recently discovered that Chinese made routers may have already placed malware in the chipset of the router to allow easier access to anyone and everyone using their products.



